Such casualties are causing immense harm to the organizations as well as the world economy. To oppose this casualty, law enforcement agencies join forces with financing regulation authorities to introduce your customer and anti money laundering for organizations. These regulations make sure that industries properly recognize their clients before directing any payments with them. Although these regulations were initiated primarily for financial institutions due to their monetary importance. Therefore, nowadays many organizations are also following these laws to enhance their security.
Over time, it has enhanced and become more precise as well as efficiency. Recently, IDV service providers have initiated digital identity verification methods that are powered by AI technology. These authentications techniques are very precise with tiny to zero chances of errors.
The requirement for customer verification mechanisms
With the existence of humanity, new digital systems have been initiated to enhance living standards. Millions of dollars are infused every day in different sectors to increase operations and work procedures. Followed by, our standard of work and way of life are enhancing with each passing day. A revolutionizing industry, information technology has emerged in our daily well-being in numerous ways. The work involving a large amount of time and manual efforts is now done within a few seconds with the aid of smart gadgets.
Like other innovations, smart gadgets can be made use of in a variety of models, as per the demand of the client. Some clients use smart laptops to their finest ability for the improvement of the globe and its residents while others utilize them to cause suffering and distress. Since the advancement of the internet, fraudsters have been deceitful and exploiting users through financial crime activities. It has become vital to hinder these fraudsters’ attacks before the damage gets more dreadful.
Two-factor authentication and its significance
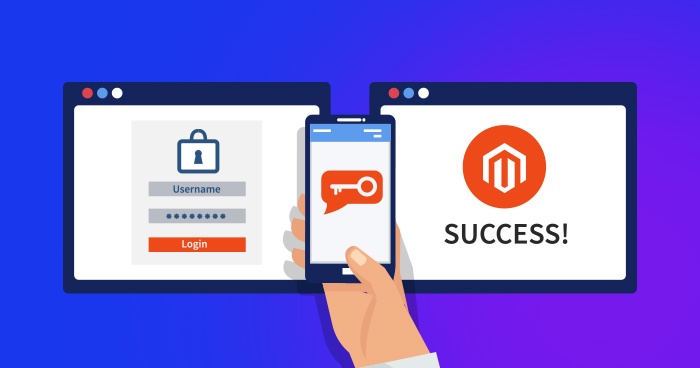
Two Factor Authentication is a security procedure that is necessary for clients to provide two different authentication models or variables to authenticate their identities. These two separate factors include something we know such as passwords, pin codes, and something we have such as authentication codes, one-time passwords sent on the client’s mobile, or email.
The two-factor authentication procedure is run out to secure the client information as well as the resources that clients gain access to. It layout an enhanced security level than other verification models that depend on one-factor verification where the client provides only one factor, usually a password or digital code. The 2FA model relies on users giving a passcode and another factor which in most cases is either a protect token or a biometric factor such as fingerprint or facial scan.
The procedure adds an additional layer of security to the authentication procedure by making it hard for a fraudster to require the authority to a client device or online account because obtaining a prey passcode and online service providers are increasingly using this procedure to safe their client’s credentials detail from being misutilization by fraudsters who have hacked a passcode database or used malicious attacks to require access to clients passwords.
The Process of two-factor authentication
- The clients are requested to access the site or platform.
- The clients provide personal information they own- usually a name and passcode then the website servers recognize the user.
- For the procedure that doesn’t require a passcode, the site generates several security keys for the client. The verification tool processes the key and the site servers authenticate it.
- The website then requests the client to perform the second login step. Here the clients have to authenticate that the procedures are something only they would have, such as safety code, Identity document, smartphone devices. The procedure is called a possession factor.
- The client then enters a one-time code that was basically done in step four.
- After successfully providing both aspects. The authentication tool processes the key and the website servers verify it.
It all adds up to
2FA is an effective way of saving clients and their possessions. The efficiency of 2FA can be known from the fact that many rising social media platforms save their clients. This will not only aid them in saving their clients from frauds but also comply with the ever-changing regulatory authorities.